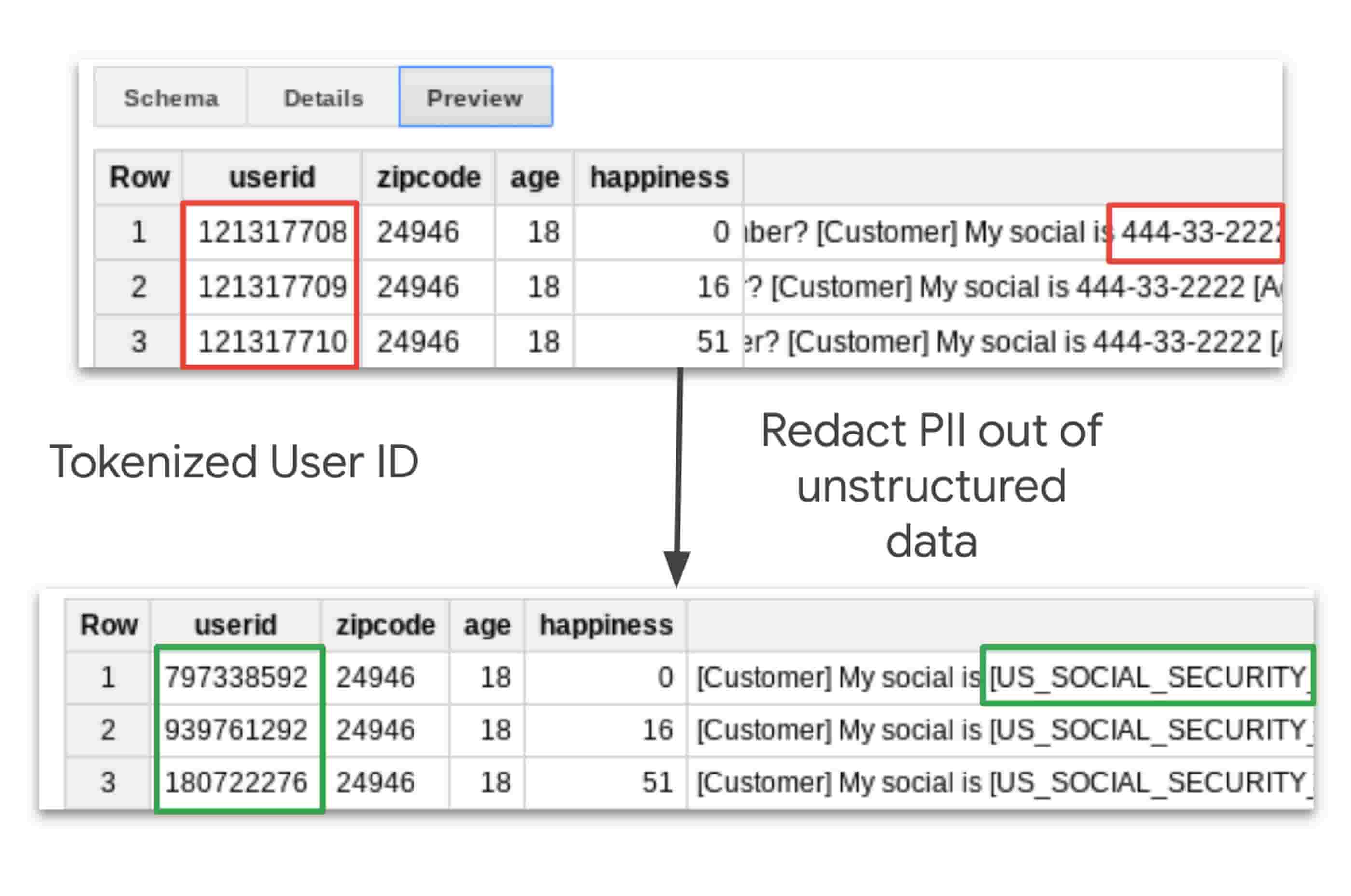
Taking charge of your data: using Cloud DLP to de-identify and obfuscate sensitive information | Google Cloud Blog
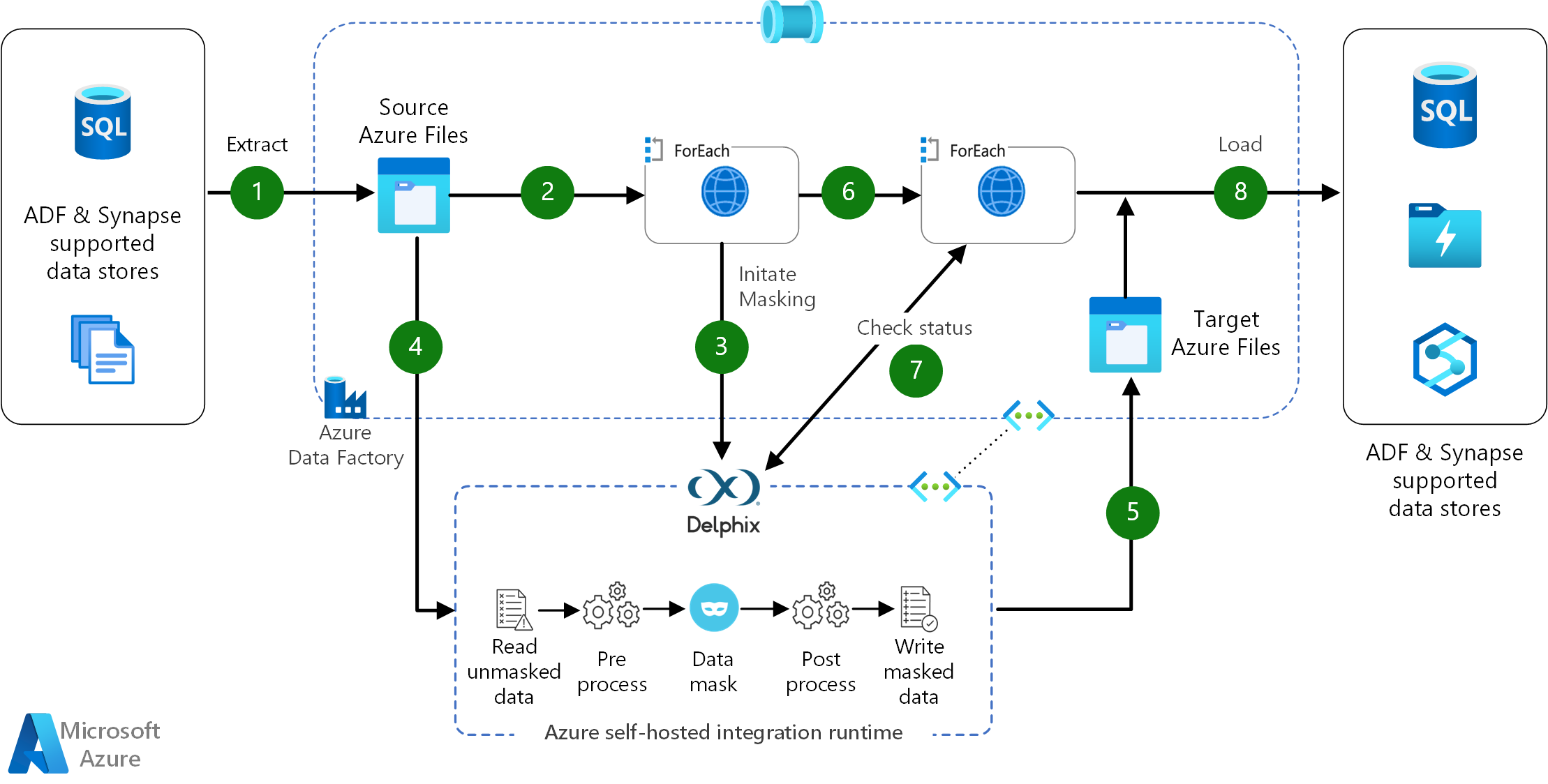
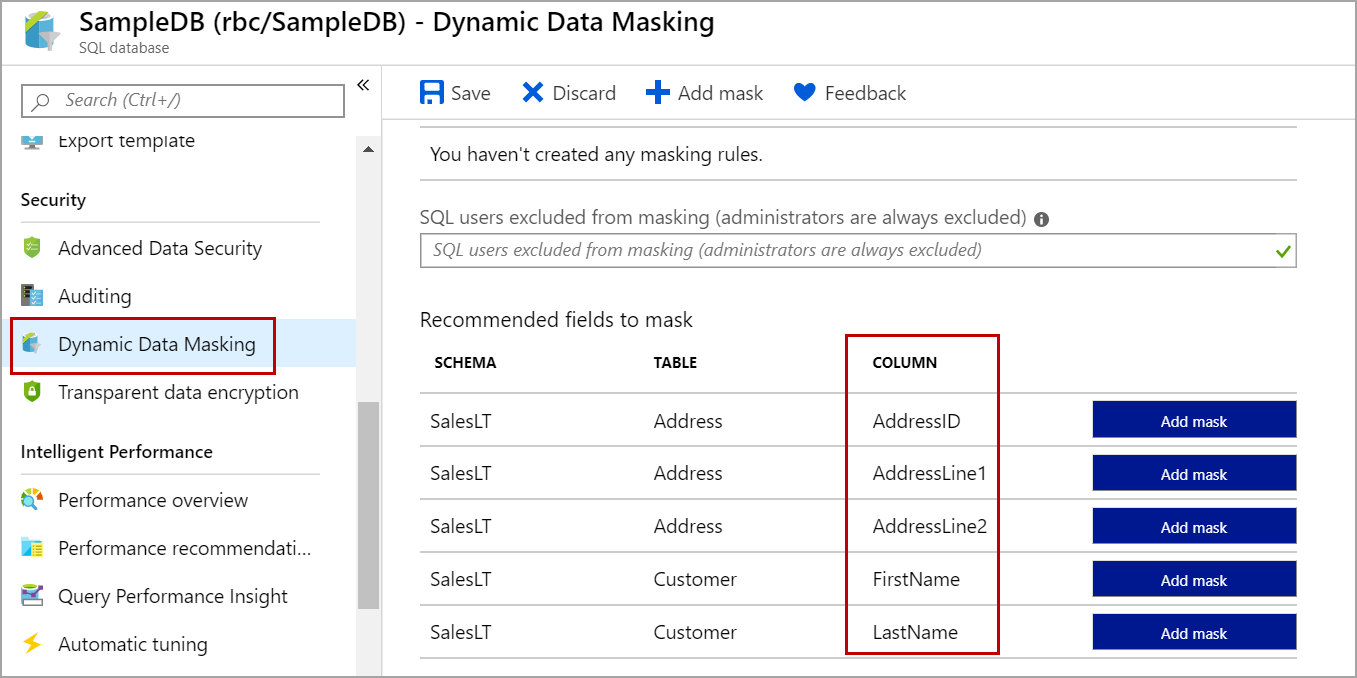
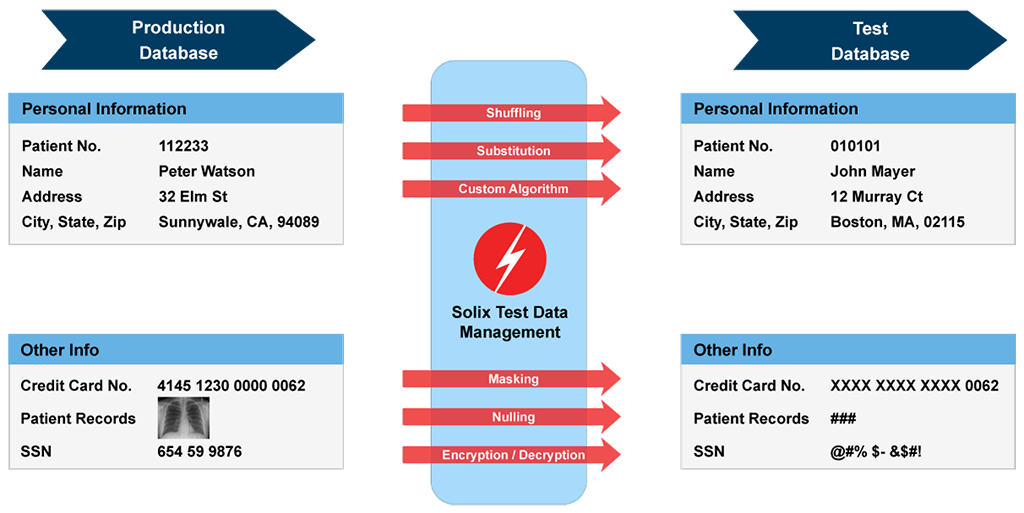
Data obfuscation using Delphix in Azure Data Factory and Synapse Analytics - Azure Architecture Center | Microsoft Learn

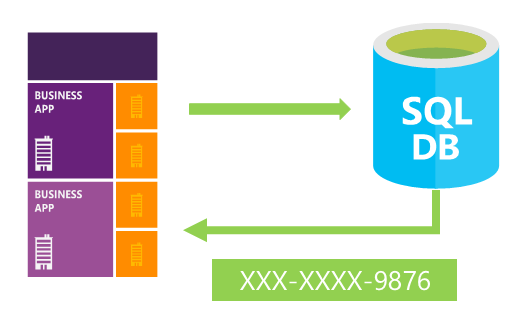
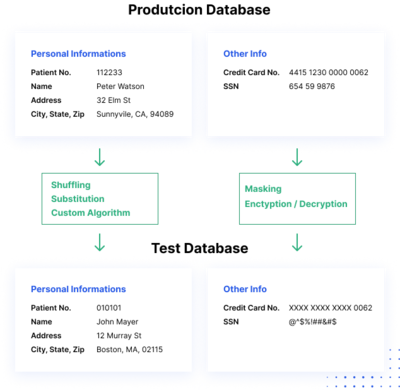
MySQL Security – MySQL Enterprise Data Masking and De-Identification | dasini.net - Diary of a MySQL experts